Port knocking has been a subject of interest to geeks, security buffs and myself for a long time. This article is the first of a serie were I’ll share my experiences and research into this field.
Port Knocking
Port knocking aims at keeping your private services even more private by keeping the door closed until someone shows up and knock on it using the secret code : “Knock knock knock knock knock, one second pause, knock knock”. It’s actually a little bit more complicated than that but at least you now know how it works.
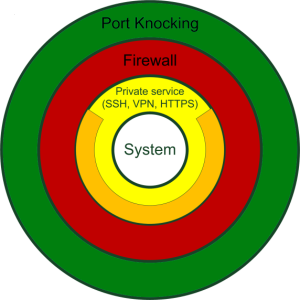
Here’s a high level view of port knocking to help you situate it within your network security onion.
Transitioning from a high level view to a close-up one, here’s how port knocking works :
The first step in implementing port knocking on your system is to setup a small program that read your firewall logs. Then you must decide what logs makes it react and what actions need to be taken. I’ll explain the action part later. The trick then is to send traffic to your firewall that makes it generate the log entries your program is looking for. The working principle is quite simple and elegant but as usual, the devil’s in the details.
What actions were you talking about?
That’s the most interesting part: You decide what must be done. The action can be anything you can program your firewall to do!
Following is an example of the simplest and most common kind of port knocking implementation which consist of opening a TCP/IP Port for a remote IP. Now, imagine that Bob wants Alice to use port knocking to connect to his private web server, here’s how he could do it :
- Bob setup his firewall with all port closed and configure it to log invalid connection attempts without replying.
- Bob setups a small daemon to read his firewall log and when the firewall blocks packets addressed to port 1234 and 12345, in that particular order and from the same IP, it opens up port 80 for the IP that has sent the packets. (The three items below will be explained in the next article.)
- The logs is the covert channel.
- The packets to port 1234 and 12345 are the knock.
- Opening up the port 80 is the action.
- Bob tells Alice in a secured manner how to knock on his firewall.
- Alice sends the knock : a packet to the port 1234 and then to the port 12345. Alice now expects the port 80 to be opened and initiates a connection to port 80.
Someone from the internet could try to scan your system for open services and fail while Alice is logging in simultaneously into your web server!
Nothing prevents you from making the daemon do something else than modifying your firewall. For example you could make it initiate a reverse ssh session or even, order a pizza…
As simple as it is in theory, in practice there are lots of gotchas that must be deal with. There’s a large volume of literature available on Internet covering different knocking methods with their pro’s and con’s. Good places to look for info is portknocking.org and wikipedia.org/wiki/Port_knocking. For a list of working implementations take a look at : http://portknocking.org/view/implementations.
You can continue your reading on port knocking with my second article on Single Packet Authorization. I’ll dig a little bit deeper this time.
Special thanks to Jerome Gauthier for reviewing this articles.